Hurricane and Tornado Hacking Protection
Equifax was hit with a Tornado, everyone else was in hurricane
by Scott Morabito
Three of the biggest news stories in the last few weeks have been Hurricane Harvey, Hurricane Irma, and the Equifax data breach.
The data breach at Equifax is somewhat unfathomable because of its scope and magnitude. Sure, there have been large hacks of data in the past such as Yahoo in 2016 and LinkedIn in 2012 – but who cares about email addresses? The Equifax breach contained identity information for 200 million Americans and this could systematically cause massive amounts of identity theft. From the outside, it would seem not that this is expected: surely Equifax had major security software, systems, and tools in place to prevent this from happening. This is certainly true. The problem with cyber attacks is the asymmetric nature of offense and defense. Protecting yourself from a data breach like the Equifax one is like building a house that can withstand an F5 Tornado.
As hurricane Harvey and hurricane Irma worked their way up the Gulf of Mexico, one thought that would go through people’s mind was “Hurricane’s have hit here before – we’ll probably be OK”. To some degree, there is some logic to this. Modern buildings can withstand hurricanes ok and can even be safe to be in during the store. Millions of people stayed in their houses during these storms and there was only a tiny percentage of life lost. There are some anomalies and bad luck associated with hurricanes, but for the most part they are survivable
When it comes to data protection, we can think of most attacks like hurricanes. Vulnerability attacks occur pervasively across the internet and “bad guys” and their bots perform routine scans and common attacks to try to gain entry. These attacks are expected and we can provide reasonable protection against them. We should expect the normal hurricane and can plan and protect against them. We can better prepare ourselves with better equipment and preparation (building on high ground). If we don’t strategize properly, expected floods and wind will affect us.
Unlike hurricane protection, tornado protection is completely different. Hurricanes are classified using the Saffir–Simpson scale and a category 5 hurricane has winds of 160Mph. Tornadoes use the Fujita scale with an F5 starting at 260Mph (3 times the wind force of a category 5 hurricane). Very little can survive an F5 simply because of the challenge and cost associated with building that level of protection. A tornado is a very targeted attack affecting a small number of people relative to a hurricane. The risk/cost factor for tornado preparation makes it somewhat impractical in most industries.
In thinking about cyber attacks, a very targeted and specific intrusion attempt on your infrastructure is like an F5 tornado touching down on your business. Organizations (except for banks and governments) typically don’t have the resources that can make them tornado proof. Run!
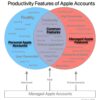
When it comes to IT Security of your infrastructure, proper and routine planning will protect against routine storms. My general advise is not to worry about the F5 tornados because even companies like Equifax are unable to guard against them. Focus your time, energy, and finances on the expected storm. Apple hardware has a lot of built in-security features and we can help ensure your Macs, PCs, iPads, and iPhones are ready for hurricane “Rainsalot” when she comes.
Scott Morabito is a technologist and founder of TechTonic. He was trained as a computer scientist and resides in Concord MA.